The Future is Digital Risk Protection
Yes, Digital Risk Protection (DRP) will move to the center of your security program. This means that DRP will be THE TOOL to help you find and take down external, public-channel threats tied to your brand, people, domains, or data.
Over the next few years, attackers will focus on your brand, executives, and customers because these targets provide the returns they’re looking for.
Your digital risk protection strategy will need to demonstrate that you can identify these campaigns early and mitigate the associated risks quickly.
Even boards will ask you to show real numbers, not promises.
AI and the future of Digital Risk Protection
AI is enabling bad actors to scale impersonation attacks, fake job ads, spoofed sites, and rogue apps. Unfortunately, security teams are in the middle of it. (Learn more: Europol IOCTA 2025)
What makes it worse?
It’s getting cheaper, simple to produce, and easy to scale.
Next-generation digital risk protection helps you spot spoofed domains, fake social media profiles, and financial fraud before moving any money.
Public channels expand your attack surface
Your attack surface now includes channels your internal tools do not watch.
Attackers use them to run scams, harvest credentials, and push false notices, so you need coverage there.
This includes:
- Social platforms
- Paid ads
- App stores
- Marketplaces
- Domains
- Forums (Learn more: Dark Web Monitoring)
For example, a paid search ad can send users to a lookalike checkout, which leads to card theft.
To prevent this, DRP will help you monitor brand terms in ads, flag new lookalike domains at registration, and route alerts to Security Teams in one workflow.
What this means for your program
DRP becomes the control layer for risks you don’t host but must manage, because those risks affect customers, revenue, and support queues.
You should track time to detect, time to takedown, and the number of cyberattacks taken down within 24 hours, by channel, so you can brief leadership with clear numbers.
Important numbers:
- Detections
- Takedowns (Learn more: What’s a Takedown?)
- Time-to-takedown
- Fraud or support cases avoided
This sets the baseline.
Next, we cover the new threats you should plan for.

New Threat At Scale That Your DRP Must Consider
These new threats start in public channels and are easy to scale, so your team needs to see them early and respond as soon as possible.
Threats to plan for with Digital Risk Protection
- Executive impersonation at scale: Cloned profiles, spoofed emails, and direct messages that trigger wires or data access.
- Deepfake fraud on live calls: Voice or video clones press teams to approve payments or share credentials. Learn more about Social Engineering Tactics here.
- Paid-ad abuse that routes to lookalike sites: Scammers buy search or social ads and harvest logins and cards.
- Account takeovers of brand or executive handles: A hijacked account posts fake updates and links that users will trust. Here’s a full Executive Protection Playbook.
- Brand abuse: Scammers copying your name, logo, visuals, and tone to look real and deceive your customers.
For example, a search ad can promote a fake “support” line during an outage. Callers reach a scam center that collects card details. To reduce losses, monitor brand terms in ads, auto-flag new lookalike domains, and route alerts to Security in one place.
Why is it harder now to build a Digital Risk Protection strategy?
Attackers can launch more convincing campaigns because AI tools lower cost and skill barriers, so volume grows across platforms at the same time.
Manual review falls behind, and fake pages or posts can reach thousands before your help desk sees the first ticket.
Realistic “from the top” requests bypass normal checks, so many teams act without a second step.
Why Digital Risk Protection is The Defence Strategy For This Shift
Digital Risk Protection sits where today’s threats start. You need it to see public-channel attacks early and take them down before they can affect your brand or customers.
Internal tools miss outside-in risk
Your stack watches mail, endpoints, and networks. It does not watch social, ads, app stores, marketplaces, or new domain registrations.
Digital Risk Protection fills that gap. It finds brand abuse, fake profiles, and leaked data where attackers stage them, not after users click.
- New lookalike domains at registration, not days later
- Fake executive or brand accounts before they grow followers (Learn more: What’s Brand Protection?)
- Paid ads that hijack your brand terms and route to phish
- Dark-web mentions of your company, data, or vendors
- Rogue apps or listings that copy your name and logo
Digital Risk Protection cuts harm and proves control
Early detection and simple takedowns reduce the time scams stay live. Less time live means fewer victims and fewer support tickets.
One workflow keeps Security, Legal, Comms, and Fraud in sync. This is great because clear owners and evidence speed decisions and takedowns.
Digital Risk Protection protects both people and systems.
- It cuts executive impersonation
- Identify and take down a lookalike domain
- Lowers “from the top” fraud.
Also, you can brief leaders with real numbers. Track what you saw, what you mitigated, and how long it took to do it. For example:
- Time to detect, by channel
- Time to takedown, by provider
- What you mitigated within 24 hours
- Executive impersonation count and repeat rate
- Fraud and support cases avoided
What Next-Gen Digital Risk Protection must include
Digital Risk Protection has to match how attackers work today. You need real coverage, clear triage, easy-to-execute and monitor takedowns, and reporting your leaders can use.
1. Unified visibility across public channels
See your risk in one place. Pull signals from domains, social platforms, paid ads, app stores, marketplaces, code repos, and paste sites.
Add deep and dark web sources, as many scams and leaks originate from these areas. Normalize and de-duplicate results, map them to owners, and estimate reach so teams can act.
Learn more: Threat Intelligence: The Ultimate Guide
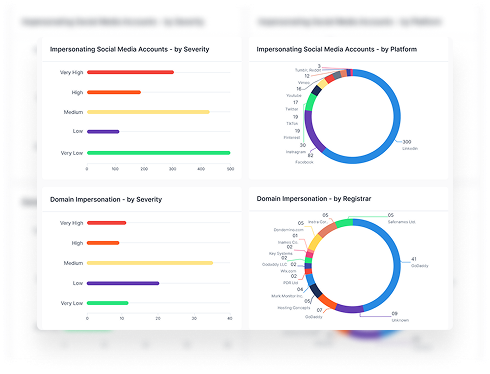
2. Brand monitoring in Digital Risk Protection
Track lookalike domains, fake apps, logo misuse, and scam ads that target your customers.
Additionally, you should be able to monitor brand terms and product names across registrars, app stores, and ad networks, then tie the findings to the relevant owners so that the right team can act quickly.
3. Fraud monitoring
DRP platforms can help you identify paid-ad abuse, fake checkouts, “support” hotlines, and refund or investment scams that exploit your name.
Moreover, it enables you to flag risky patterns, such as new payment instructions, unusual checkout flows, or cloned onboarding pages, and route high-risk cases to Security and Fraud with clear evidence.
4. Social and news media intelligence
Monitor social platforms and news sites for mentions, fake affiliation, and hurtful coverage tied to your brand or products.
DRP enables you to detect posts that spread sensitive data or false claims, track how they spread, and give Comms and Legal the context they need to respond.
5. Executive / VIP protection
Identify impersonation of leaders across social, email, and messaging. Alert on fake profiles, spoofed domains, and direct messages to staff or partners.
Detect doxxing, harassment, and threat language, and escalate to the right owners when safety or legal risk appears.
Learn more: Executive Protection Hygiene: The Playbook
6. Data leakage and dark web monitoring
Find exposed credentials, code, documents, and customer data on paste sites, forums, and marketplaces.
Map items to systems and owners, trigger resets where needed, and track recurrence by actor and source.
Learn more: The Essential Guide to Data Leakage
7. Takedown services
Submit and track takedowns across hosts, registrars, social platforms, and app stores from a single workflow. Learn more about Brand Impersonation Takedowns here.
Important things you should see here:
- Status
- Case IDs
- SLAs
- Capture screenshots, URLs, timestamps, and more
- Easy submission
- Proof of removal
- Reporting
After that, watch for re-registration so you can respond if the actor returns. Keep an audit trail and evidence pack for legal follow-up and board reporting.
What You Should Do Now For Digital Risk Protection
Start with moves that increase visibility and speed up response. Digital Risk Protection works when you map what’s official, watch the right signals, and act in one workflow.
1. Inventory your digital footprint
List every asset that customers, staff, or partners might use. Keep it in a place teams can reach and keep it current.
- Primary and secondary domains, subdomains
- All email sending domains and mail providers
- Official social handles, exec handles
- Mobile apps and publishers
- Marketplaces and seller accounts
- Support sites, phone numbers, and emails
2. Create watchlists and close spoofing paths
Build watchlists for brand terms, product names, exec names, and high-risk vendors. Include common misspellings and regional variants.
Set thresholds for alerts. Route brand abuse to Security and Legal immediately, and copy Comms when customers may be affected.
3. Set owners, runbooks, and evidence standards
Name clear owners. Security runs operations, Legal approves actions, Comms handles notices, and Fraud tracks customer impact.
Write short runbooks for the top five cases: fake site, fake profile, fake ad, exec threat, vendor leak. Keep steps simple and assign SLAs.
Define evidence once. For each case, capture URLs, screenshots, headers, WHOIS, platform case IDs, and timestamps. Store it where all owners can access it.
4. Drill account takeovers and brief leadership
Run a quarterly drill for brand and executive account takeovers. Test detection, access recovery, and public messaging, end to end.
After each drill or live case, update the runbook and evidence checklist. Close gaps.
Brief leaders with one page: detections, takedowns, time to takedown, what you mitigated, and any fraud or support cases avoided.
What to Measure For Digital Risk Protection (Friendly, Useful, Board-Ready)
Digital Risk Protection makes a difference when you can show clear numbers.
Keep it simple, consistent, and tied to decisions.
Metrics that prove control
Track how quickly you find threats in public channels, and how fast you mitigate them. Time drives harm, so make it your headline.
Breaks down results by channel and provider. A platform view shows where you need escalation paths or a stronger takedown template.
Make it board-ready
Leaders want trend lines and outcomes, not raw counts. Show quarter-over-quarter deltas and a short note on what changed.
Keep the report to one page. Add links to evidence packs for anyone who needs detail, and keep definitions stable across quarters.
Collect clean data without heroics
Instrument the workflow. Every detection and takedown should create a ticket with timestamps, owner, evidence, and a case ID.
Tag cases by threat type, channel, actor recurrence, and impacted brand or region. This makes your scorecard roll up without manual work.
Scorecard essentials
- Time to detect (median), by channel (social, ads, domains, app stores, dark web).
- Time to takedown (median), by provider or platform.
- % mitigated within 24 hours, trended monthly, by channel.
- Executive impersonation count and repeat rate for known actors.
- DMARC enforcement coverage across all sending domains.
- Customer impact avoided: fraud refunds prevented, support tickets reduced, chargebacks averted.
Drop vanity metrics like raw alert totals without action, and sentiment charts without a follow-up step.
The Platform You’ll Need: AI-Driven Digital Risk Protection At Scale
An AI-driven Digital Risk Protection platform eliminates manual work and cuts time-to-takedown.
Here’s how to make it easier and faster for your team.
1. Automation that replaces manual monitoring
The platform should watch the open web, dark web, social platforms, messaging apps, app stores, forums, and file-sharing sites in one place.
It should use AI, pattern recognition, and real-time search to spot lookalike domains, fake profiles, leaked data, and threat chatter as they appear.
It should also map your digital footprint so findings tie back to owners and systems without spreadsheets.
2. Risk scoring and routing you control
Use a risk score that weighs impact, exposure, and urgency, so you work the highest-risk items first. Let teams adjust weights to reflect customer reach, payment exposure, and executive risk, without a services ticket.
Auto-route high-severity items to Security, Legal, and Comms with clear owners and SLAs. This keeps the response fast and repeatable.
Learn more: Risk Scorecard: The Secret Behind the Numbers
3. Integrated takedowns and evidence
Launch takedown requests to registrars, hosts, social platforms, and app stores from the same screen, then track status, case IDs, and timestamps to closure. Include screenshots, URLs, and headers in an evidence pack for each action.
Export weekly ops reports and an executive one-pager with detections, removals, and time-to-takedown by channel. Keep an audit trail for legal follow-up.
Styx solutions that make this faster
- Brand Monitoring + Social & News Monitoring: Detect lookalike sites, scam ads, fake profiles, and adverse media linked to your name.
- Executive Protection: Catch impersonation, spoofed domains, doxxing attempts, and accounts that target staff and partners.
- Data Leakage and Dark Web Monitoring: Find exposed credentials, documents, or databases tied to your company or vendors.
- Third-Party Vendor Risk: See supplier leaks, breach history, and mentions early… then trigger outreach and containment.
- Attack Surface Management: Keep an accurate asset map so alerts resolve to the right owner.
- Threat Intelligence + Risk Scorecard + Takedown Service: Enrich findings, score what matters, and take down fake assets with proof of action.
Together, these capabilities turn noisy public signals into clear actions your team can take in minutes, not days.
Want to learn more about Styx Intelligence? Book a demo with our team.