Credential stuffing is when attackers use stolen usernames and passwords to break into accounts.
They do not guess passwords. They use login details that have already leaked from past breaches, then test them across websites, apps, customer portals, and employee tools.
This works because many people reuse passwords. If one account gets exposed, attackers can try the same login on other services.
For your business, this is critical.
One reused password can lead to account takeover, fraud, data theft, and support costs. It can also damage trust when customers blame your brand for an account compromise that started somewhere else.
This guide explains how credential stuffing works, why it matters, and how your team can defend against it.
How Does Credential Stuffing Work?
Credential stuffing starts with leaked login details.
Attackers collect usernames and passwords from past breaches, malware logs, forums, and dark web markets. Then they use bots to test those credentials across many login pages at once.
The typical attack flow includes:
- Acquiring credential lists from data breaches or dark web sources
- Deploying bots or proxy networks to test these credentials across multiple sites simultaneously
- Identifying valid logins.
Once attackers gain access, they can steal data, conduct fraud, or sell accounts on the black market.
Credential stuffing is effective because even a low success rate becomes profitable at scale. They focus on the external digital footprint to exploit weak points and gain unauthorized access without needing to randomly guess passwords.
Credential Stuffing vs Brute Force Attacks vs Password Spraying
All these have the same objective, which is to identify working login information and exploit it, however, they work differently.
Credential stuffing
Attackers use stolen username and password pairs from past leaks.
They test those real credentials across other sites to see where people reused passwords.
Example: An attacker finds a leaked email and password from an old shopping site breach. They try the same login on your customer portal.
Brute force attacks
Attackers try to guess the right password for one account (without previous knowledge).
They use many password guesses, often based on common words, names, or patterns.
Example: An attacker targets one admin account and tries thousands of password guesses until one works.
Password spraying
Attackers try a few common passwords across many accounts.
This helps them avoid account lockouts because each account only gets a small number of attempts.
Example: An attacker tries “Spring2026” across 5,000 employee accounts.
The key difference is this:
Credential stuffing starts with passwords that already worked somewhere else. That makes it harder to spot than basic guessing, especially when attackers spread attempts across many IPs, devices, and locations.
Why Are Credential Stuffing Attacks Increasing?
Credential stuffing is growing because attackers have more stolen passwords than ever.
Every breach adds new username and password pairs to breach lists, forums, and dark web markets. Attackers take those credentials and test them across ecommerce sites, social platforms, financial services, customer portals, and employee tools.
The attack works because password reuse is still common. If someone uses the same password across 3 accounts, one breach can give attackers access to more than one service.
Automation makes the problem worse.
Bots can test huge credential lists at scale. Proxy networks help spread login attempts across many IP addresses and locations. Some tools can also bypass basic checks such as CAPTCHA or simple rate limits.
For businesses, the damage shows up in different ways:
- More account takeovers
- More password reset requests
- More fraud reviews
- More customer support costs
- More customer trust issues
- Brand reputation damage
- More pressure on security and fraud teams
Customers often do not know where their passwords first leaked. They only know their account with your company was compromised.
That makes credential stuffing a brand problem, not just a login problem. Your team needs a way to spot exposed credentials early, understand which accounts are at risk, and act before attackers turn stolen passwords into working access.
The Consequences of Credential Stuffing Attacks
Credential stuffing can look like a login issue at first. It rarely stays that small.
Once attackers gain access to real accounts, they can use them for fraud, data theft, resale, or more targeted attacks.
The impact usually falls into 5 areas:
- Account takeover: Attackers access customer, employee, or partner accounts using stolen credentials.
- Financial fraud: Compromised accounts can be used for purchases, transfers, refunds, loyalty point theft, or payment changes.
- Data and regulatory exposure: Attackers may view or steal personal data, payment details, order history, internal files, or private messages. This can affect compliance with data protection laws, resulting in fines and legal action.
- Brand damage: Customers often blame your company when their account is abused, even if the password first leaked somewhere else.
- Operational cost: Your team has to handle password resets, fraud reviews, support tickets, investigations, and customer notifications.
The harder part is scale.
Credential stuffing can affect many accounts at once, and attackers often move before your team sees the full pattern. That makes fast detection and clear response steps critical.
How to Detect Credential Stuffing Attacks
Credential stuffing is easier to stop when your team catches the signs early.
Watch for patterns such as:
- Many failed login attempts from one IP address or region
- Fast login attempts across many accounts
- Successful logins from unusual locations or devices
- Login attempts that use credentials found in known leaks
- Spikes in password reset requests or account lockouts
These signals often show that attackers are testing stolen usernames and passwords at scale.
Threat intelligence helps your team add context. It can show whether exposed credentials are tied to your company, where they appeared, when they were leaked, and what type of data was exposed.
That context matters. If employee or customer data appears on forums, breach lists, or dark web markets, your team can reset accounts, block access, and alert affected users before attackers cause more damage.
Early detection gives your team a chance to act before credential stuffing turns into account takeover.
How to Prevent Credential Stuffing
To prevent credential stuffing, your team needs controls that stop stolen passwords, slow automated login attempts, and flag risky access before accounts are taken over.
Start with these controls:
| Multi-factor authentication (MFA) | MFA adds another login step, which reduces the success of automated credential attacks. |
| Enforce unique passwords | Encourage or require users to create unique passwords for each account; password managers ease this burden. |
| Use bot detection | Look for signs of automation, such as repeated login attempts, unusual device patterns, proxy use, and high-volume traffic. |
| CAPTCHA and challenges | CAPTCHA can help in some cases, but attackers can bypass it. Use it with other controls, not as your main defence. |
| Watch for exposed credentials | Monitor breach lists, malware logs, forums, and dark web markets for credentials tied to your company. |
| IP and proxy blocking | Identify and restrict traffic from known proxy services or malicious IP ranges. |
| Account lockout and throttling | Apply adaptive rate limits and temporary lockouts to suspicious login attempts. |
| Security awareness | Make password reuse easy to understand. Show employees and customers why one leaked password can put other accounts at risk. |
No single control stops credential stuffing on its own.
MFA reduces successful logins. Bot detection slows automated testing. Dark web monitoring helps your team find exposed credentials before attackers use them. Together, these controls make account takeover harder and give your team more time to act.

How to Recover from Credential Stuffing Attacks
When you detect credential stuffing, you must move quickly. Your goal is to cut off access, protect affected users, and find out what attackers did.
Use this response flow:
- Force password resets on compromised accounts: Immediately require new credentials to prevent persistent access.
- Revoke active sessions: Terminate sessions established by attackers to disrupt ongoing access.
- Investigate and remediate: Audit logs to identify impacted users and detect post-compromise actions such as data theft.
- Communicate transparently: Notify affected users with clear guidance on password changes and security practices. Clear communication fosters customer trust and supports collective security awareness, reducing the risk of future incidents.
- Strengthen controls: Immediately enforce MFA, increase bot detection sensitivity, and review security policies.
- Coordinate across teams: Work with security, IT, fraud, and customer support teams to mitigate impact and prevent recurrence.
- Strengthen controls after containment: Review what failed. Add MFA where it is missing. Improve leaked password checks, login monitoring, and alert rules.
After the attack, document the timeline, affected accounts, attack sources, response actions, and gaps. This gives your team a clearer playbook for the next attempt.
Protect Your Business’s Reputation from Credential Stuffing Attacks
Credential stuffing starts with exposed credentials, but the damage can reach your customers, your support team, your fraud team, and your brand.
Styx helps your team detect leaked credentials before attackers use them. Monitor breach lists, malware logs, forums, and dark web markets for employee, customer, and company-linked data.
When exposed credentials appear, your team can see:
- Which accounts may be at risk
- Where the credentials appeared
- When they were first seen
- What type of data was exposed
- Which response steps should happen next
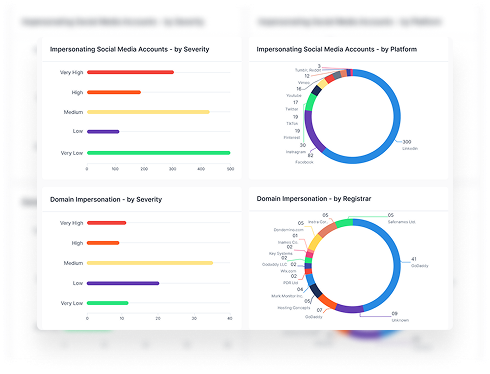
Styx also helps you track the wider risks that often come with credential abuse, including fake login pages, lookalike domains, phishing sites, and impersonation attempts.
Book a demo to see how Styx helps detect exposed credentials, protect accounts, and reduce brand risk.