CISO and Cyber Teams
Digital transformation is creating new vulnerabilities and threats that security teams struggle to handle. Use StyxView to maintain full coverage of your attack surface and internet-facing systems to proactively counter malicious actors.
Defend Your Company Against Incoming Threat Vectors
The transition to remote working has increased cyber threats such as ransomware, DDoS, and data leakage. These continuously complex challenges are becoming more difficult for internal security teams to mitigate themselves. Today’s tools lack the wide visibility and sophistication needed to effectively counter attackers.
Use StyxView to reduce the burden of monitoring for threats by taking advantage of our coverage of the surface, deep, and dark web. Prioritize cases with our digital risk score to establish what’s exposing you the most.
Identify Configurations and Misconfigurations of Assets
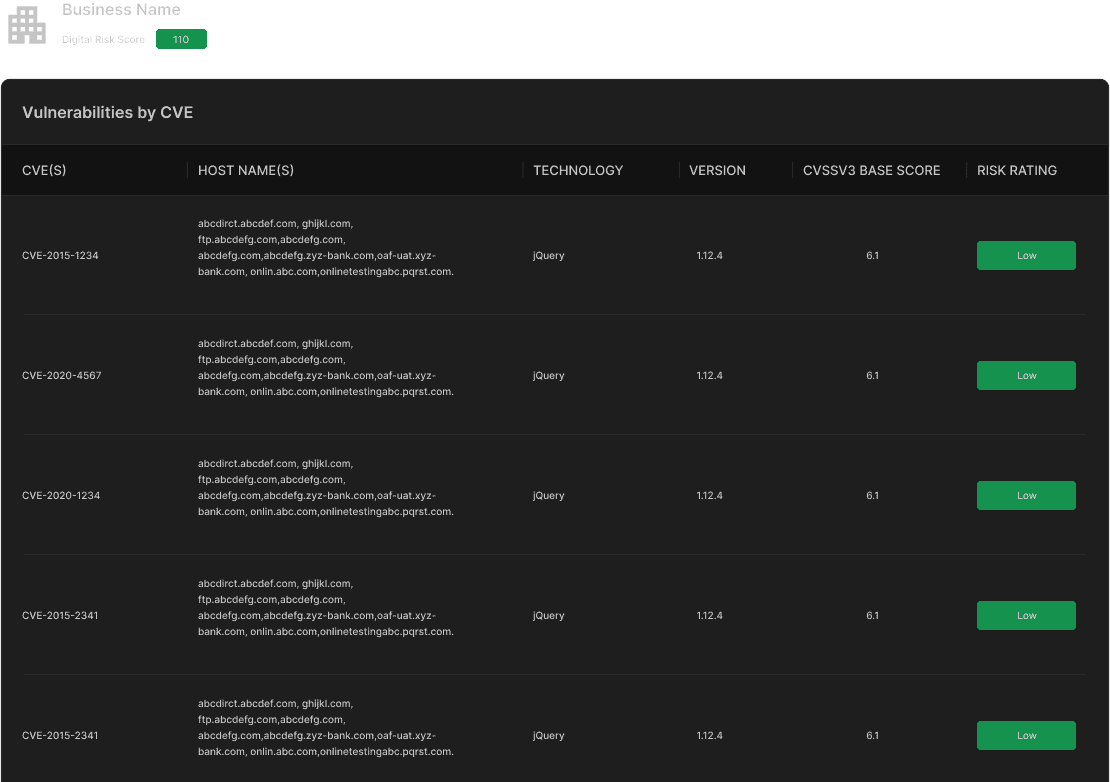
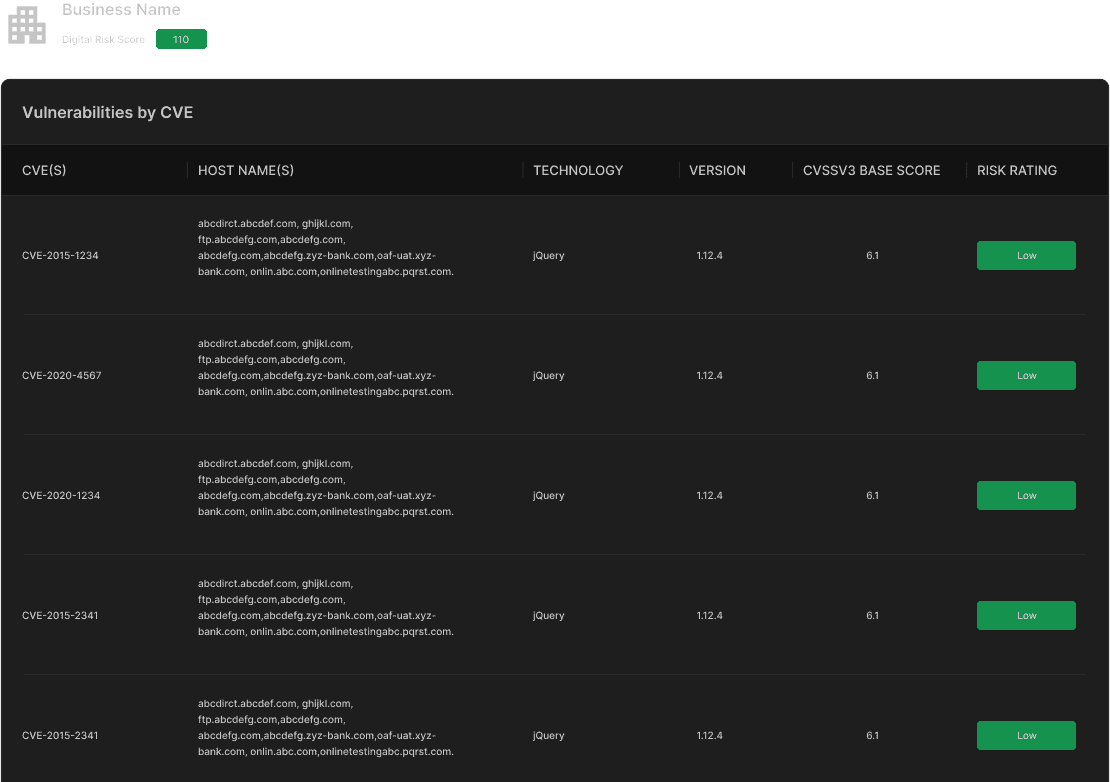
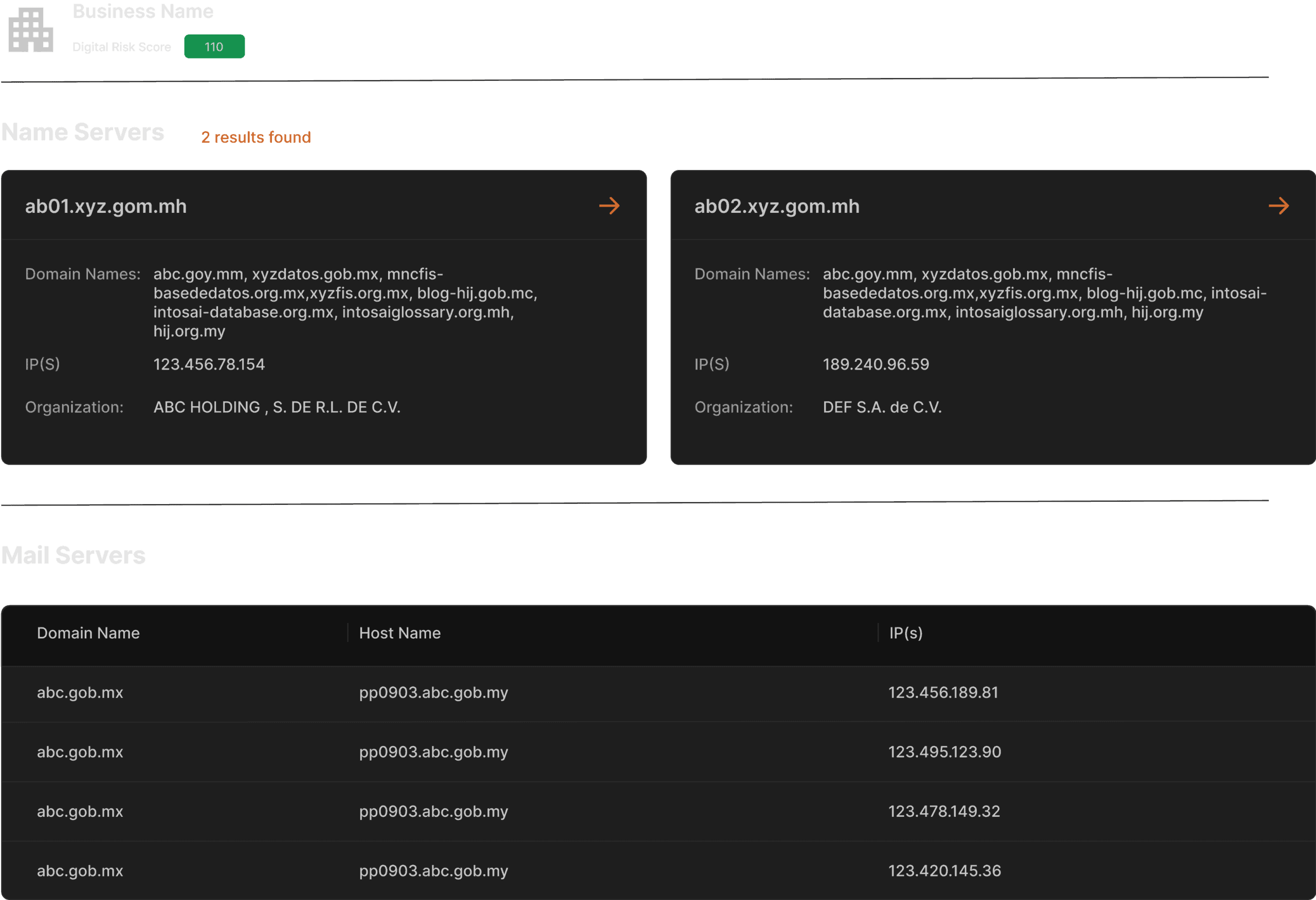
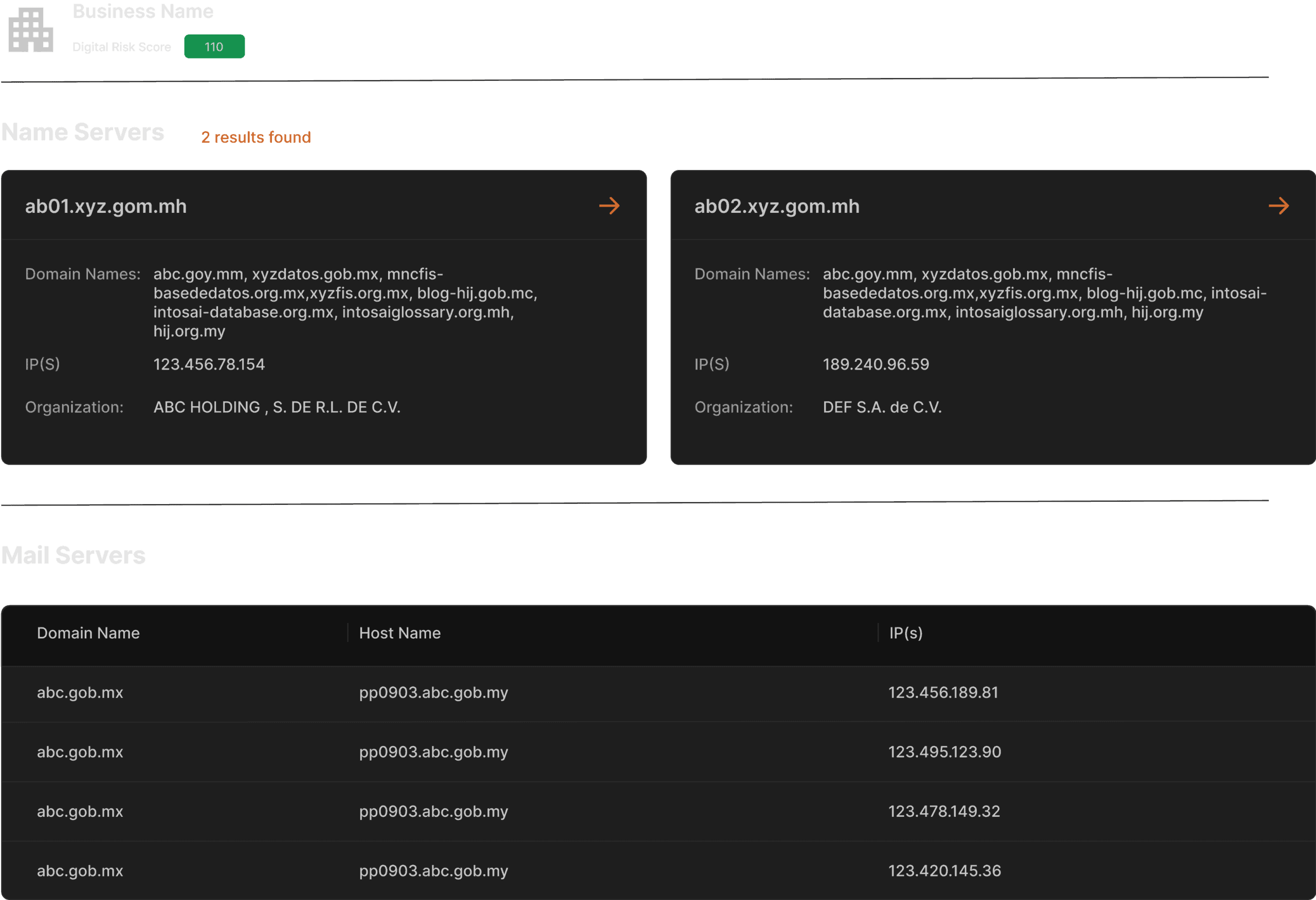
As a CISO, you know the importance of proactively identifying potential weaknesses in you organization’s internet-facing digital assets. StyxView takes an attacker-perspective approach to uncover exposed assets and sources that need protection. From identifying CVEs to detecting misconfigured web servers, StyxView delves deep to provide the insights you need to tighten your security protocols.
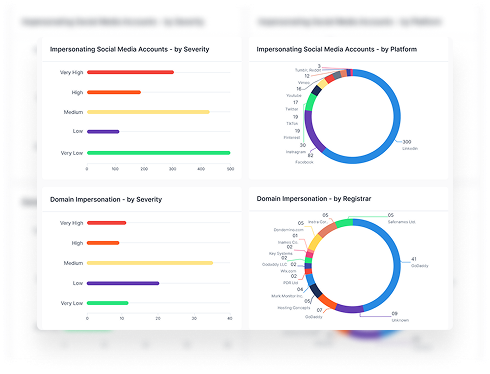
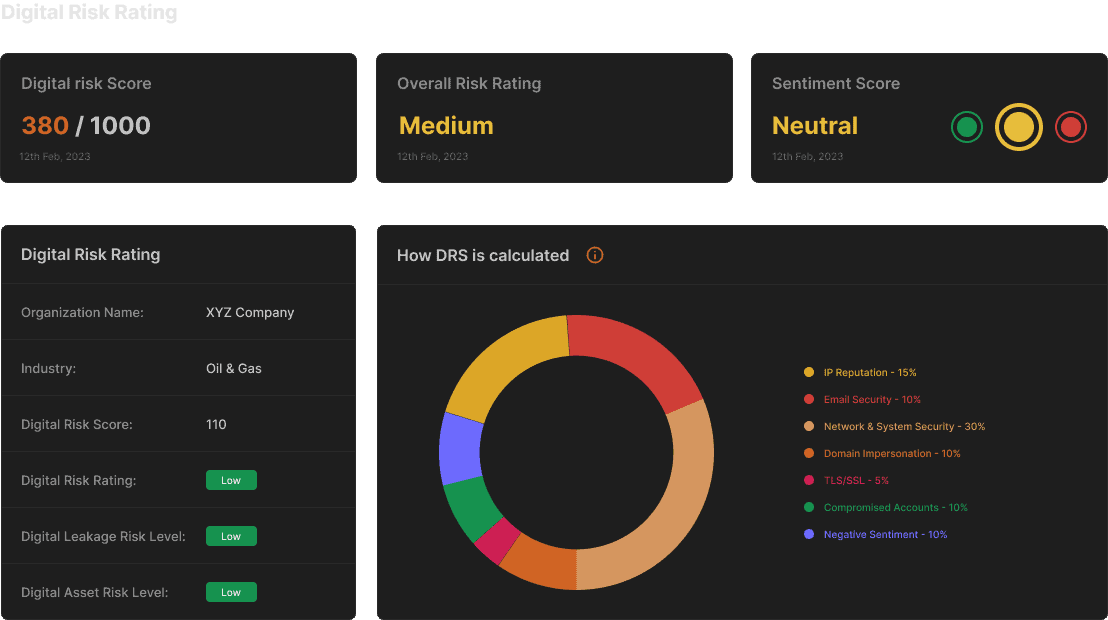
Prioritized Risk
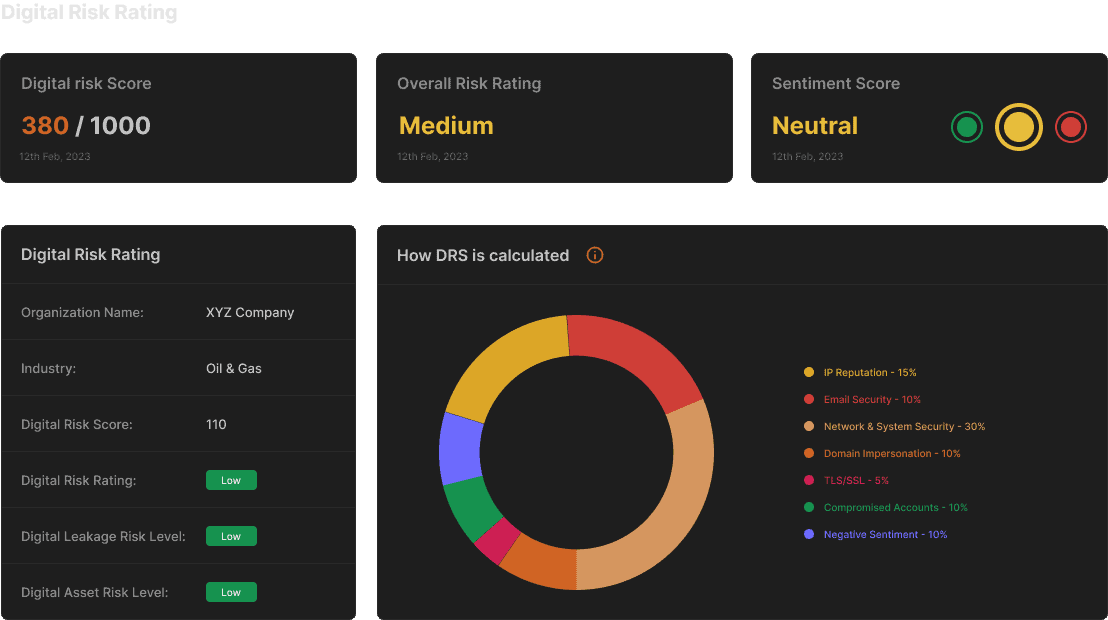
StyxView’s risk-based approach simplifies understanding your company’s external security posture. Our digital risk score considers multiple factors such as host domains, mail servers, third party application usage, and data leakage with severity classification. This contextualizes your score so that you can quickly identify and prioritize areas that require attention.
Guidance on Best Practices for Remediation
Identify the most critical threats to your company’s security using StyxView’s dashboard. Our risk scoring system provides a comprehensive overview of your cyber posture, allowing you to prioritize remediation efforts with confidence. Our expert team is here to guide you through understanding your unique circumstances and provide tailored advice on managing your digital footprint.
See StyxView in Action
Book a Demo
Explore Solutions for CISO and Cyber Teams
External Exposure Management
Real-time visibility into your organization’s digital exposure, helping you proactively manage new risks created by increasing digital connectedness.
External Data Leakage Detection
Monitor the surface, deep, and dark web for compromised credentials, exposure of sensitive documents, code repositories, cloud storage, and other data leaks.
Third Party Risk
Streamline due diligence on vendors with security scorecard and automated third-party questionnaires.